Rules
We ask that you respect the following rules and guidelines. Repeated violations will lead to disqualification from the bounty program.
-
All bug reports need to have clear reproduction steps and/or proof of concept.
-
Submit one vulnerability per report, unless you need to chain vulnerabilities to provide impact.
-
Any type of public disclosure of the vulnerability without prior approval from the bug bounty program will make it ineligible for payout.
-
Please inform us if you have your own timeline for full disclosure (90 days minimum). Unless specified we will release the information at our own pace.
-
All Current/Past (for up-to 6 months) Decred contractors are barred from taking part in this bug bounty program.
-
You must not leverage the existence of a vulnerability or access to sensitive or confidential data to make threats, extortionate demands, or ransom requests.
-
Hazardous testing without explicit authorization will lead to disqualification. This includes:
- Issues relating to excessive traffic/requests (e.g. DoS, DDoS)
- Attacks which may affect the availability of systems
- Social engineering attacks (e.g., phishing, opening support requests)
- Attacks that are noisy to users or admins (e.g., spamming notifications or forms)
- Attacks against physical facilities
-
Content generated by LLMs must be meaningfully edited, validated, or supported by original analysis. Reports consisting primarily of low-effort, irrelevant, or excessively verbose content will be rejected.
Reminders
-
Almost all of Decred’s projects can be run locally and reproduction instruction are available on GitHub. We strongly recommend you to do this.
-
There is a completely separate Decred testnet which is specifically created for software testing. Testing on the public testnet will prevent impact on mainnet and removes the risk of causing real financial damage. It is also possible to create your own personal simnet, running on your own local system with low enough difficulty to mine blocks using only a CPU.
-
Always check the “issues” in GitHub of a project to avoid a duplicate report.
-
Decred project is not responsible for any loss of DCR due to bug testing.
Payout
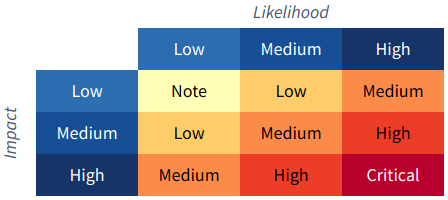
The OWASP Risk Rating Methodology will be used for assessing vulnerabilities and determining payout amount.
The impact on the Decred ecosystem will also be taken into consideration. An RCE in dcrwebapi (low impact) is not the same as an RCE in dcrd or Decrediton (higher impact). The payout amount is decided by a core “bug bounty” group. Once decided, there will be no changes to the payout amount unless the vulnerability impact changes.
The following are also factors in the payout:
- Quality of the initial writeup.
- Quality of vulnerability reproduction steps and/or proof of concept.
The bounty program is funded by the Decred Treasury, therefore all payments are in DCR only. Recipients are required to create a Decred wallet and provide a payment address. Payouts are sent at the beginning of each month using the average DCR/USDT rate of the previous month.
For vulnerabilities that require a patch rollout and pose a risk to the network participants, we might choose to only release 60% of the payout amount first and hold the 40% until a patch has been released and distributed.
The maximum approved budget for the payouts is capped at 100,000 USD. Please be aware of this when you are submitting multiple critical vulnerabilities. If the limit is reached then a new proposal will have to be submitted and get stakeholder approval before you get paid fully.
The bounty hunter will be given one month to claim it after which the bounty will be considered forfeit.
Indicative payout amounts
Note: up to 500 USD
Low: up to 1,500 USD
Medium: up to 5,000 USD
High: up to 15,000 USD
Critical: up to 30,000 USD






